Abstract
This chapter details the importance of architectural thinking and design in developing a digital video surveillance or physical security system. It outlines the process from requirements gathering to network implementation and provides insight into the value of a lead architect, who accepts accountability for the technical solution through the iterative process of definition and execution.
Keywords – Architecture , architecture , design, dynamic , process requirements , process, improvementsite, surveys documentation, deliverables.
Related terms:
Enterprise Architecture , Architecture Design, Enterprise application , Information System Security , Security Officer
Solution Architecture and Design Process
The solution architecture and design process phase (see Figure 1) determines how to best design the solution, choosing the depth of the project, the schedule, hardware, and software to best satisfy both project and business requirements.
This is also where the team determines how the integration (hardware and/or software) of any required physical security subsystem into a single interface can improve efficiencies and decisions and reduce cost and risk. An architectural team is assigned, with architects, subject matter experts, and engineers from various disciplines, hardware and software vendors, and the customer.
This team works iteratively to determine success criteria, goals and objectives, and budget restraints as well as update project requirements and new procedural details, if necessary, and to document the architectural conceptual design and develop a presentation detailing the viability and benefits for key executives to obtain cost approval.
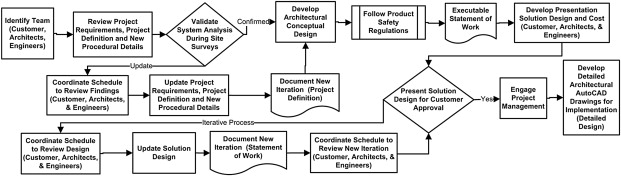
As previously mentioned, there should be a lead architect—an individual who understands all the pieces of the puzzle to some capacity and who can listen to the wealth of information available from the team, because too many chefs in the kitchen can become a disaster, and no one likes playing the blame game, so a single point of accountability for the technology decisions is best practice.
Solution Architecture
The practice of solution architecture becomes more granular than enterprise architecture and takes into account decisions made at the enterprise architecture level. After an application has been determined as a fit within the enterprise and its appropriate business capability areas defined, a determination must be made on how exactly to implement the enterprise application. This is where solution architecture comes into play.
To clarify, solution architecture does involve other work as it relates to implementing applications into corporate environments. In many cases, it is the recommendation of solution architects based on their analysis of business requirements that will lead to the examination of specific enterprise applications for potential fit within the company.
Just like many other roles in information technology, there are many aspects to the role of solution architects and those aspects involve working with architecture solutions in two directions. One is from the project direction where business requirements are documented and the solution architect must determine how to meet those requirements.
This can, naturally, involve the possibility of implementing new enterprise applications to meet those requirements. The other angle is from the implementation direction where it has been determined that a specific technology or enterprise application must be implemented and the solution architect must figure out how. It is this latter aspect of the solution architecture role that we will be focusing on as it is most applicable to enterprise applications administration.
With that in mind, we know at this point the application that needs to be implemented, the functionality that it provides, and the business capabilities that are impacted by that functionality. In addition, we know what other enterprise applications exist within those business capabilities already and may have some direction from the enterprise architecture perspective on how to handle any conflicts.
For this example, let’s assume that the only business capability where there is a true conflict of functionality is that of the SAP application in the Fulfillment business capability. The direction from the enterprise architecture practice within the organization is to leverage the existing SAP enterprise application and the modular design of FLARP will support this.
With organizations that have a solution architecture practice whether standalone, as a part of the enterprise architecture group, as part of a business capability silo, or as a part of a dedicated development organization, it is the function of this practice to map out how an enterprise application should be logically implemented within the corporate enterprise.
To do so, the solution architect takes into account the functions of the enterprise application, the data that it needs in order to operate, where that data comes from, where it needs to go to, and any external functions that the enterprise application needs to leverage in order to meet the requirements provided by the business. With this data, the solution architect develops a map of how the new enterprise application should fit into the landscape of existing enterprise applications.
Going through this process, the solution architect first gains an understanding of what the enterprise application does and how it does it. Frequently, this will involve working closely with application developers, vendors, and enterprise applications administrators in order to gain as much information about the application as possible. The solution architect needs to know what logic the enterprise application uses when making decisions, what the inbound and outbound data is, and how the application operates at a functional level. This will guide the solution architect on how they can integrate the new enterprise application within the corporation.
Another critical component is understanding what external functions the enterprise application needs in order to work properly. We know already that it needs to integrate to SAP for order fulfillment. But what about the credit check? Does it need to contact a credit agency to perform that check and then interpret the results? Does the order data need to make it into a reporting system for analytics purposes? What if an order is canceled due to a failed credit check or the customer changes their mind? Should those orders be put into another system for future marketing purposes? Finally, does the application have all of the data it needs about the customers, services, product offerings, service areas, and everything else associated with its functionality internally, or does it need to contact other applications to get more information?
It is the practice of solution architecture which is intended to figure out the answers to all of these questions and put together a design that illustrates an overall solution to the implementation. This solution can then be analyzed and approved by the enterprise architecture practice within the company or guidance can be provided on alternative solutions that more closely align with the company’s longer term business strategy. As always, the development of this or any architecture is a collaborative effort across many people with their own areas of expertise.
Figure 2 shows one possible solution architecture model for the FLARP application. In this architecture, the FLARP application has links to a number of additional applications in order to receive or send data. These interfaces are illustrated with the requesting system using the “open arrow” side of the line and the responding system using the “closed arrow.” For example, FLARP requests information from the Credit Check service and the Credit Check service will respond with the information FLARP needs. Note that at this point the types of interfaces have not been defined nor have the individual servers or network components associated with the enterprise application. All of these aspects of the enterprise application will be defined as we go through the application and technical architecture designs.
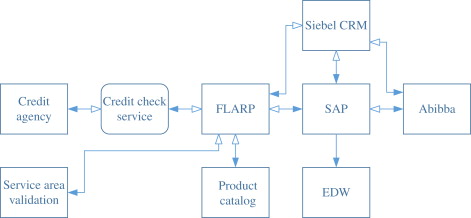
The solution architecture shown in Figure 2 draws out a much more detailed view than those used at the enterprise architecture level. The focus has now moved beyond categorization and into the realm of interaction. Solution architecture is all about making sure that the appropriate enterprise applications are able to interact with each other in the best way possible in order to make efficient use of enterprise resources. This also lines up with the enterprise architecture goals of reducing costs and complexity. At the solution architecture level, the guidance provided at the enterprise architecture level begins to manifest itself into the implementation process.
In many cases, there are dozens of ways that a given enterprise application can be implemented within an enterprise, each of which has its own pros and cons. The solution architect takes a look at each approach and makes the best decisions that they can based on the functionality of existing systems, the ability of those systems to conform to the needs of the new enterprise application, the cost of system modification or interfaces, the source of record for any given data element, the requirements defined by the business, and the long-term business capability roadmaps defined by the enterprise architecture practice. In some cases, making these implementation decisions may involve consulting with experts on individual technologies or enterprise applications including other architects or enterprise applications administrators.
When the solution architecture is being defined, it’s important to start thinking about how security fits into the enterprise application’s architecture. In many organizations, there is a security architect who can work with the solution architect to help ensure that the overall solution complies with the enterprise’s security policies and industry best practices. There is generally not a separate architecture document associated with security architecture. Instead, the results of the security architecture work are incorporated into the other architectural documents. In some organizations, the security architect will also provide a review document of some type detailing their assessment of the architecture. It’s of critical importance that security be a part of every portion of an enterprise application’s architectural design.
In the end, the solution architect should develop an approach similar to that shown in Figure 6.4 that can then be used as a map for building out the implementation of the enterprise application. In some cases, the solution architect may develop multiple options along with a list of pros, cons, and costs associated with each option. It then generally falls to collaboration between the business stakeholders, architects at all levels, company executives, and occasionally enterprise applications administrators to agree to implement one of the defined options. After that decision is made, all of the groups must commit to supporting it and the next two levels of architecture can be developed.
Enterprise architect case study
Shailesh Kumar Shivakumar, in Architecture High Performing, Scalable and Available Enterprise Web Applications, 2015
This chapter examines an end-to-end architecture solution for a case study. In chapters related to scalability, availability, and performance, we have seen case studies specially targeted for those individual chapters. This chapter extends those concepts, and we will look at a close-to-real-world scenario and architect a solution to satisfy the specified nonfunctional requirements, focusing especially on scalability, availability, performance, and security. We will start with design considerations, integration methods, and major architecture decisions, which lays out the initial platform, and then we will add the scalability, high availability, and high performance features to satisfy the specified requirements.
We will see a practical application of the process steps, methodologies, and models that we saw in the first three chapters. At the end, we will look at the final overall logical architecture and the risk and mitigation strategy. This case study is designed to reinforce the concepts learned in earlier chapters and to make the readers aware of the practical application of those concepts through step-by-step examples. Though this is a fictional case study, technical aspects such as integration methods and nonfunctional requirement specification are designed to closely mimic real-world scenarios.
Miscellaneous
James V. Luisi, in Pragmatic Enterprise Architecture, 2014
Pragmatic Enterprise Architecture
What makes enterprise architecture pragmatic?
First, it is important to know what enterprise architecture is. It is not solution architecture for the enterprise, where without frameworks one individual is supposed to provide specialized technology advice across business and IT any more than a physician is supposed to provide specialized medical advice across the townsfolk. Rule number one is that EA is not a GP practice, as that would rapidly lead to architectural malpractice.
Just as physicians who specialize in various highly technical areas and their specialized staff support a medical center, enterprise architects provide expertise and services to business leaders and solution architects, who in turn deliver care directly to the home of an application team, or set of application teams.
One of the most valuable aspects of having specialists co-located together in a medical center is that they are better able to collaborate. Similarly, once enterprise architects collaborate with other enterprise architects of different specialties, they discover the synergies that exist and recognize new ways of looking at issues and approaching them, perhaps with much greater effectiveness.
What may be most challenging is if the local tribe has never seen a medical center before, it is likely that they will not understand what a medical center is, what it does, how it works, and what its value proposition is. This issue is not that uncommon when it comes to growing organizations with an emerging need for an EA capability. To such an organization, the role of a true EA capability will sound theoretical, where it is action that they want as if action could be supported by one general practitioner given the role of “chief enterprise architect.”
The less likely challenge is that the growing organization knows what an EA practice is, they realize that they need the services of a mature enterprise architecture practice, but don’t have one yet and need to get one. Normally, the folks in small towns go to a nearby city to get the services and expertise they need as they need them. Hence, the city medical center supports the city plus all of its neighboring towns for any specialty services that a GP would not be able to address.
Similarly, enterprise architecture can be supported by a consulting firm that specializes in the various architectural disciplines that comprise EA, however few of these consulting firms presently exist, and few of those have the breadth of skills that would be tuned to meet the specific needs of the large organization. Enterprise architecture practices are tuned to the organization just as medical centers establish the skills most commonly needed by the population in their geographic area, whether that includes specialization for snake bites, tick bites, altitude sickness, or hypothermia.
Other important dimensions of what constitutes enterprise architecture are that as a technology medical center it provides a significant amount of preventive care. There are numerous known illnesses that culminate from certain inadvisable technology practices, and EA can help the organization establish the healthy behaviors that prevent these expensive and complex automation diseases.
Most importantly, however, pragmatic enterprise architecture is opportunistic. As issues arise across a large organization, or as awareness of issues emerges due to an insightful enterprise architect or senior manager, it presents an opportunity to establish an architectural discipline, its frameworks, and its assorted collateral to help guide solution architects going forward. As architectural disciplines get built out, their specialized personnel are either delivering a good ROI, or they are not. As in any business, you reduce overhead as you find ways of supporting the capabilities required using alternate means.
Pragmatic enterprise architecture as such is essentially a pragmatic medical center that provides services that reduce technology costs in personnel, software licenses, and computing hardware and infrastructure acquisition. Once an organization is mature and knows how to avoid unnecessary technology complexity and costs, then fewer or different enterprise architects can be considered.
TOGAF ®️
Philippe Desfray, Gilbert Raymond, in Modeling Enterprise Architecture with TOGAF, 2014
Architecture and solution
For TOGAF readers, one item of vocabulary still has to be explained. TOGAF often refers to solution architecture. Here, the term “architecture” designates a description, and more precisely a logical view, as opposed to the “solution,” which represents a technical reality. This distinction can be clearly seen in the terms “Architecture Building Block” and “Solution Building Block” (respectively ABB and SBB). The logical specification of an element is an ABB, while its physical equivalent is a SBB. These two types of element are present in the architecture repository, which enables either the documentation or the physical component to be reused, according to the context.
Big data processing architectures
Infrastructure
To process data other than structured and additional volumes to current data, a combination of heterogeneous technologies is recommended. The solution architecture will include the following type of technologies:
Hadoop, NoSQL, or similar data processing platforms, driven on nonrelational and file system–based architecture.●
MapReduce programming model will be implemented for managing data processing and transformation.●
Data discovery and analysis will be implemented using Tableau or Datameer software that abstracts the complexities of MapReduce and works directly on Hadoop for data integration and management.●
Analytics on Hadoop will be implemented using R, Predixion, and other competing technologies capable to MapReduce integration and management.●
In-memory data processing solutions like Qlikview need to be tested further for advanced reporting requirements, depending on the success and adoption of the new stack of technologies.●
Hardware infrastructure will be running on a commodity platform based on multicore processors and up to 96 GB RAM.●
Disk architecture for the new infrastructure will be not based on storage area network (SAN) but on direct attached storage (DAS).●
A redundant configuration will be set up for failover.●
A landing zone will be available on the existing server with unlimited storage. The storage will be designed for high capacity and not for high performance.●
Security for the raw data will be implemented on current disk storage access policies.●
Security rules for nonrelational data postprocessing will follow the existing rules in the LDAP repository (integrated single sign on security process) for EDW data.
Infrastructure
To process data other than structured and additional volumes to current data, a combination of heterogeneous technologies is recommended. The solution architecture will include the following types of technologies:
●Hadoop, NoSQL, or similar data processing platforms, driven on nonrelational and file system–based architecture.
●MapReduce programming model will be implemented for managing data processing and transformation.
●Data discovery and analysis will be implemented using Tableau or Datameer software that abstracts the complexities of MapReduce and works directly on Hadoop for data integration and management.
●Analytics on Hadoop will be implemented using R, Presented, and other competing technologies capable to MapReduce integration and management.
●In-memory data processing solutions like Qlikview need to be tested further for advanced reporting requirements, depending on the success and adoption of the new stack of technologies.
●Hardware infrastructure will be running on a commodity platform based on multicore processors and up to 96 GB RAM.
●Disk architecture for the new infrastructure will be not based on the storage area network (SAN) but on direct attached storage (DAS).
●A redundant configuration will be set up for failover.
●A landing zone will be available on the existing server with unlimited storage. The storage will be designed for high capacity and not for high performance.
●Security for the raw data will be implemented on current disk storage access policies.
●Security rules for nonrelational data postprocessing will follow the existing rules in the LDAP repository (integrated single sign on security process) for EDW data.
Storage design validation
Pierre Bijaoui, Juergen Hasslauer, in Designing Storage for Exchange 2007 SP1, 2008
Publisher Summary
A proof-of-concept phase should be included in a Microsoft Exchange project schedule. This testing phase allows verifying whether the theoretical assumptions were valid and the proposed solution architecture will meet own or customer’s requirements.
Several tools are available to test the configuration, starting from low level disk exercisers like IOmeter, to an Exchange Store process simulator, and at the upper end a tool that simulates the actions users perform when they read and send emails or meeting requests.
Start the design validation by testing the storage environment before running a test that simulates users accessing the Exchange environment using Outlook Anywhere via ISA arrays and hardware load balancers. One should check to see whether the firmware and device drivers of the components used by Exchange servers are reliably working together.
It is recommended to run tests in a test environment and not in a production environment. Separating the test environment from the production environment removes the risks that tests impact production systems. Low-level tools such as disk exercisers do not require a lot of prerequisites; full installation of the Exchange environment is not necessary—it is sufficient that the storage subsystem is connected to a Windows host. Therefore, they can be easily used to get results in a short timeframe.
The IOmeter tool measures performance of network I/O and I/O to a disk subsystem. The tool allows one to characterize disk subsystem performance without the need to set up the complete infrastructure that the application requires. Regarding an Exchange mailbox server, one needs the server and the storage array, but does not need the Active Directory (AD) and the other Exchange server roles to verify disk array performance. Microsoft Exchange Server JetStress simulates disk I/O that the Exchange Store process performs. With JetStress one can check whether the system configuration will likely be able to handle the transactional workload generated by user activity with acceptable latency figures.
ISCM Architecture
An ISCM architecture documents continuous monitoring processes, information needs, functional and technical requirements, and supporting tools and technologies, either alone or as an element of agency enterprise, solution, or security architectures.
The architecture provides a consistent point of reference across all levels of the organization for implementing continuous monitoring capabilities, and documents services, technologies, processes, and tools available as common controls to information systems. Federal guidance does not mandate a standard ISCM architecture, but NIST cites the Department of Homeland Security’s Continuous Asset Evaluation, Situational Awareness, and Risk Scoring (CAESARS) [7] as an example and has proposed an extension to the CAESARS framework potentially applicable to all federal agencies as a technical reference architecture for continuous monitoring [33].
Any purpose-specific technical architecture should integrate with broader agency security architecture and enterprise architecture models, especially to link technical monitoring capabilities to enterprise risk management and other mission and business functions that monitoring supports. Ee
ARCHITECTURE : foundation service
How does HP design service architecture?
When customers ask HP to help them design service architecture, we use the HP Global Method for IT Strategy and Architecture (HPGM for ITSA, formerly CSAM). This approach to creating enterprise and solution architectures has proved effective through many years
experience in defining, guiding, and evolving complex information systems in multiple application domains. Our consultants and customer stakeholders participate in developing a four-view model:
▪Business view: Why is the project being done? What are the motivations and business drivers?
▪Functional view: What will the system do? What information will it provide?
▪Technical view: How will the system be realized with IT components?
▪Implementation view: With what specific products and other components will the system be implemented? In what organization? According to what plan?
HPGM defines each view using principles, models, and standards appropriate for the business domain. When combined, the four views let us understand the needs of all stakeholders and create a snapshot of what the solution should look like
An extensible framework of methods, tools, and techniques supports this methodology. It is the foundation for a standard set of architectural services with well-defined deliverables across multiple scopes (discrete project, initiative, and enterprise). (See Table 5.3)
Table 5.3. Primary components of HP Global Method (HPGM)
(HPGM) Description
Project Management
HPGM is the methodology for defining project management based on more than 30 years of experience from Hewlett-Packard and Compaq. It is consistent with the Project Management Institute’s (PMI, http://www.pmi.org)
A Guide to the Project Management Body of Knowledge (PMBOK®)—2000 Edition, (December 2000)IT Strategy & Architecture (formerly CSAM) ITSA is the framework for structuring architectural descriptions and an integrated, complementary set of services that are characterized by shared stakeholder understanding and commitment, clearly demonstrable business value and low development risk.
IT Strategy & Architecture (formerly CSAM) ITSA is the framework for structuring architectural descriptions and an integrated, complementary set of services that are characterized by shared stakeholder understanding and commitment, clearly demonstrable business value and low development risk.Application Development Application development provides a versatile and expanding range of methodologies that address the many types of application development, including a classic waterfall approach and a distributed objects methodology.
Application Development Application development provides a versatile and expanding range of methodologies that address the many types of application development, including a classic waterfall approach and a distributed objects methodology.Implementation Implementation contains proven, widely used IT service management (ITSM) based on the industry-standard IT Infrastructure Library (ITIL), including the mature Rapid Solutions Delivery.
Implementation Implementation contains proven, widely used IT service management (ITSM) based on the industry-standard IT Infrastructure Library (ITIL), including the mature Rapid Solutions Delivery.
Integration includes the Services Oriented Application Lifecycle (SOAL), plus Package Integration, Data Warehousing, B2E (business to employee), and CRM (customer relationship management) and the Systems Engineering Delivery Framework.
Support contains the Service Delivery Guides and Technical service kits (Source: Hewlett-Packard) RIoT Control
Tyson Macaulay, in RIoT Control, 2017
Reference architecture
The primary purpose of a reference architecture is to guide and constrain the instantiations of solution architectures. The knowledge, patterns, and best practices gained from those implementations are incorporated into the reference architecture. The reference architecture also describes the major foundational components such as architecture building blocks for an end-to-end solution architecture.
Metrics of a properly implemented reference architecture are:
•Evolutionary: How easy was it to revise to include new insights?
•Reusability: How well did it help your organization in accelerating delivery of solution architectures through the reuse of an effective solution?
•Governance: Did it effectively promote the governance to ensure the consistency and applicability of technology use within an organization?
•Repeatability and consistency: Was it really effective and detailed architectural information in a common format such that solutions can be repeatedly designed and deployed in a consistent, high-quality, supportable fashion?
So what exactly is a reference architecture?
It is a generalization of multiple solution architectures that have been designed and successfully deployed to address the same types of business problems or use case.
It is a predefined architectural pattern, or set of patterns, possibly partially or completely instantiated, designed, and proven for use in particular business and technical contexts, together with supporting artifacts to enable their use.
A reference architecture shows how to compose these patterns together into a solution. It can be a set of multiple reference architectures within a subject area where each represents a different emphasis or viewpoint of that area.
It can be defined at many different levels of detail and abstraction (from specific to generalized) and for many different purposes. It consists of a list of functions and some indication of their interfaces—or application programming interfaces (API)—and interactions with each other and with functions located outside of the scope of the reference architecture.
How is a reference model used? It serves as a reference foundation for architectures and solutions, as a template solution for an architecture for a particular domain; as a framework for scope identification, gap assessment, and risk assessment to develop a roadmap to design and implement a solution; and as a source for common vocabulary with which to discuss implementations, often with the aim to stress commonality. A reference model further serves as a tool to accelerate delivery through the reuse of an effective solution and as a basis for governance to ensure the consistency and applicability of technology use within an organization.
Privacy policy
We use cookies to help provide and enhance our service and tailor content and ads. By continuing you agree to the use of cookies.
Copyright © 2022 The artistic marketeer or to its licences


